Global Manhunt Pushes Limits of Social Mobilization
Network of Spotters Tracks Suspects through Social Media in Simulated Jewel Heist in Five Cities across North America and Europe
Published Date
Article Content

A map showing how researchers expect people to recruit participants
An international team of researchers, including computer scientist Manuel Cebrian from the University of California, San Diego, has won a seemingly impossible challenge: tracking down a group of “suspects” in a jewel heist on two continents in five different cities, within just 12 hours. The goal was to find five suspects. Cebrian’s group, named CrowdScanner, found three. That was far better than their nearest competitor, which located just one “suspect”—at a much later time.
It was all part of the “Tag Challenge,” an event sponsored by the U.S. Department of State and the U.S. Embassy in Prague that took place March 31. The challenge aimed to “determine whether and how social media can be used to accomplish a realistic, time-sensitive, international law enforcement goal.” With a $5,000 reward for the winners, the goal was to build a network of spotters and teammates for the simulated law enforcement search through social media in each of five cities including Washington D.C., New York City, London, Stockholm and Bratislava in Slovakia.
In the end, the winning team’s strategy—to publicize their work in mainstream media as well as through social media channels, including Facebook and Twitter—prevailed. This is not Cebrian’s first win in seemingly impossible conditions. In 2009, he led the team that successfully located 10 weather balloons scattered through the United States in just nine hours, as part of a challenge sponsored by DARPA. The Tag Challenge was much harder, he said.
“These kinds of competitions help us scientists understand how social networks form and evolve,” Cebrian said. “They help us understand things like the Arab Spring and the Occupy protests. They allow us to collect a lot of data that would be otherwise impossible to have access to.”
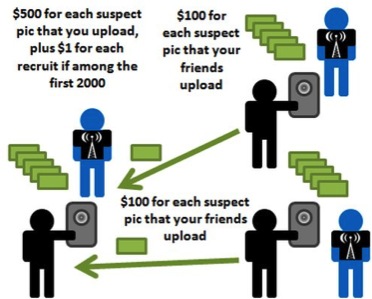
How the rewards scheme works
For the Tag Challenge, organizers posted on their website a “mug shot” of each suspect on the day of the event. Each suspect was wearing a shirt bearing the event logo. The suspect’s face, dress and the contest logo were clearly visible in each of the mug shots. Contestants could use only this photograph and any other information provided on the event website to identify each suspect. The goal was to find and photograph all five suspects. Organizers verified that the photos were real by checking for a unique code phrase on both the front and back of the shirt the suspects wore, which was not revealed in their suspect’s mug shot but known only to the organizers.
Cebrian’s team promised $500 to those who took winning pictures of the suspects. If these people had been recruited to be part of CrowdScanner by someone else, that person would get $100. To help spread the word about the group, people who recruited others received $1 per person for the first 2,000 people to join the group.
Before the day of the challenge, he and colleagues conducted several interviews with reporters, trying to get their story into as many media outlets as possible. One of the items made it onto the popular news aggregating site Slashdot. Researchers also spread the word through CrowdScanner’s Facebook page and Twitter account. In hindsight, Cebrian said, after preliminary examination of empirical data, he believes mainstream media sites were 100 to 1,000 times more effective to spread the word than individuals spreading the word through social media. Cebrian's approach received numerous accolades, including from Prabhakar Raghavan, a vice president of engineering at Google and the former head of Yahoo! Labs.
The day of the challenge, Iyad Rahwan, the team’s leader and a researcher at the Masdar Institute of Technology in Abu Dhabi, set up a war room in the United Arab Emirates. He and developers were up on deck by 10 a.m. Surprisingly, the first winning picture came fairly quickly from Bratislava, where a team of computer scientists from a local university had heard about CrowdScanner through Slashdot. One of the scientists saw the Bratislava “suspect” and sent them a picture. Cebrian’s team hadn’t expected to make headway in the Slovak capital, where many people don’t speak English.

"Suspects"
Then around 1 p.m. Eastern, a graduate student from Harvard, who had heard about CrowdScanner from a mailing list, found the New York “suspect” in Grand Central Station. He too sent the researchers a winning picture.
Then things got quiet until 7 p.m. Eastern. At that point, David Alan Grier, the president-elect of IEEE and a professor at George Washington University, was on his way home from work. He had heard about CrowdScanner from a mailing list too. The Washington, D.C., suspect was pictured with a giant coffee mug. To Grier, that meant she would probably be found in a coffee shop. He decided to check a few coffee places out on his way home. He caught her and photographed her as she was leaving a coffee shop. “In the world of computer science, it’s as if Barack Obama had taken the winning picture,” Cebrian said.
His team was never able to find the London and Stockholm suspects. At this point, they’re waiting for competition organizers to release data about the suspects’ itinerary that day. That would allow them to understand how they caught three of the five.
“We’re excited to get the whole picture,” Cebrian said. “Social networks are not a silver bullet. We need to better understand their limits.”
Share This:
Stay in the Know
Keep up with all the latest from UC San Diego. Subscribe to the newsletter today.